After many months of work, I’m happy to share that our NSO Bookable Sandbox and NSO Always-On Sandbox have received a well-deserved upgrade. NSO sandboxes are a great companion when you’re on the path to automation and when you need a quick environment to test your ideas. And the best part is that NSO Sandboxes are free to use! It’s as simple as making a reservation, pressing the start button and you’re ready to go.
Now let’s take a look at the upgrade we have prepared for you.
NSO Always-On Sandbox
The NSO Always-On sandbox has been migrated to the official NSO container. We built on top of the container to ensure that the sandbox is always available and easy to update and manage.
The NSO router package has been installed (this package is taken from the NSO built-in examples) and we can see the basic environment using Netsim.
This sandbox is read-only, which is intended for quick viewing and simple tests, such as API calls to synchronize devices with NSO. If you want an environment where you can get your hands dirty, read on.
Sandbox with NSO reservation
NSO’s exclusive sandbox is where you want to test your ideas and break things. You now have three instances of an NSO installation that are great for high availability scenarios, among other things.
Again, the secret of these three instances is in the official NSO container, which we used to add all the packages, NEDs and configurations required at build time. So when you start the sandbox, you will have NSO instances ready in a deterministic state.
If you’re interested, check out the NSO Containers Reservable Sandbox where we’ve posted the scripts, Dockerfile, and configuration used to build this container.
CML topology
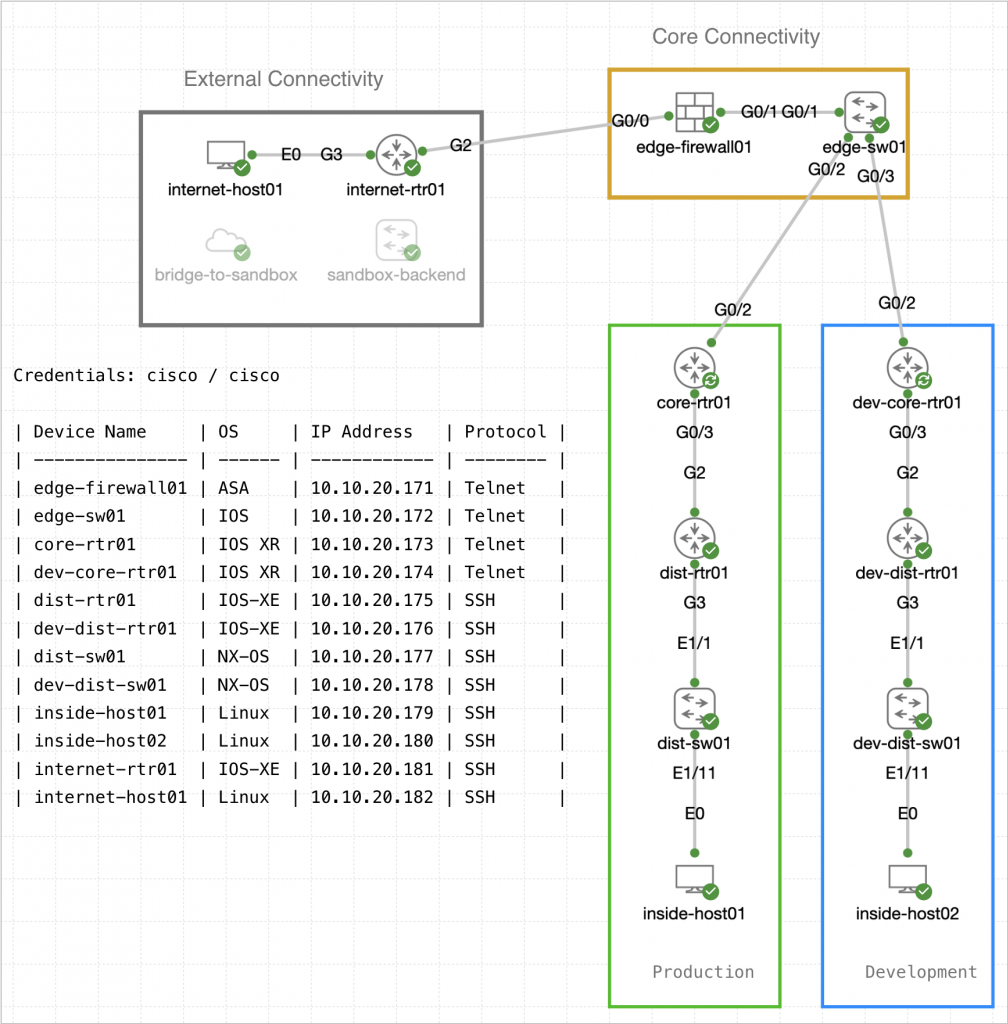
However, only NSO instances were not updated. The CML topology has also undergone changes and corrections. You will now find a topology consisting of several network devices and hosts that emulate two networks, one for development and one for production.
You can communicate with devices directly using TELNET/SSH or via NSO. NSO instances have a minimum required configuration to work with them.
This topology is great when you want to use a pipeline that tests development and deploys to production.
GitLab
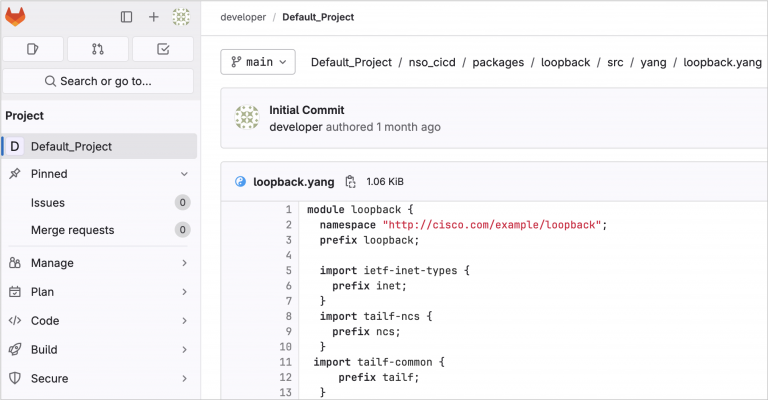
Speaking of channels, the GitLab instance inside the sandbox has also been upgraded to a newer version of GitLab. You can also find a demo project (thanks to the Cisco CSS CX Automation team) and a GitLab run ready to use with the pipeline. An example will come soon.
What will happen next?
We have many ideas of what we could add and upgrade to the sandboxes, as well as add examples that can use them to their full potential. But I’m more interested in what you think we should add next, what you need or what you’re interested in.
You want to know more
Here are some links to save (or save this blog) to learn more about NSO.
Want more content about NSO? Contact me on LinkedIn. I love hearing your ideas.
Share:
